Could your business withstand a cybersecurity attack? Do you have a cybersecurity plan for your business in place?
While no one is completely immune from cyber attacks, there are ways to avoid becoming a cyber attack victim.
Cybersecurity experts reveal the threat of online crime has never been greater, with scam artists, hackers, and criminals targeting everything from your personal information to your bank account. It’s not only consumers who are at risk: Businesses large and small have also become targets for criminals looking to steal data and money.
And SMBs are particularly at risk.
Identify the threats and understand the risks
“The common misconception is, ‘It’s not going to happen to me. It’s happening to the big guys, and I’m not a big guy. Why would they ever come after me?’” said Marc Pickard, Co-founder/CEO of CB Tech Support.
As technology advances, the risk of security breaches also increases. Keeping financial data and confidential information safe and secure must always remain a top priority for any business.
Whether it’s data security and storage, management of transactions, or simple payment processes, it’s important to prioritize cybersecurity so as not to compromise the integrity of financial platforms and services.
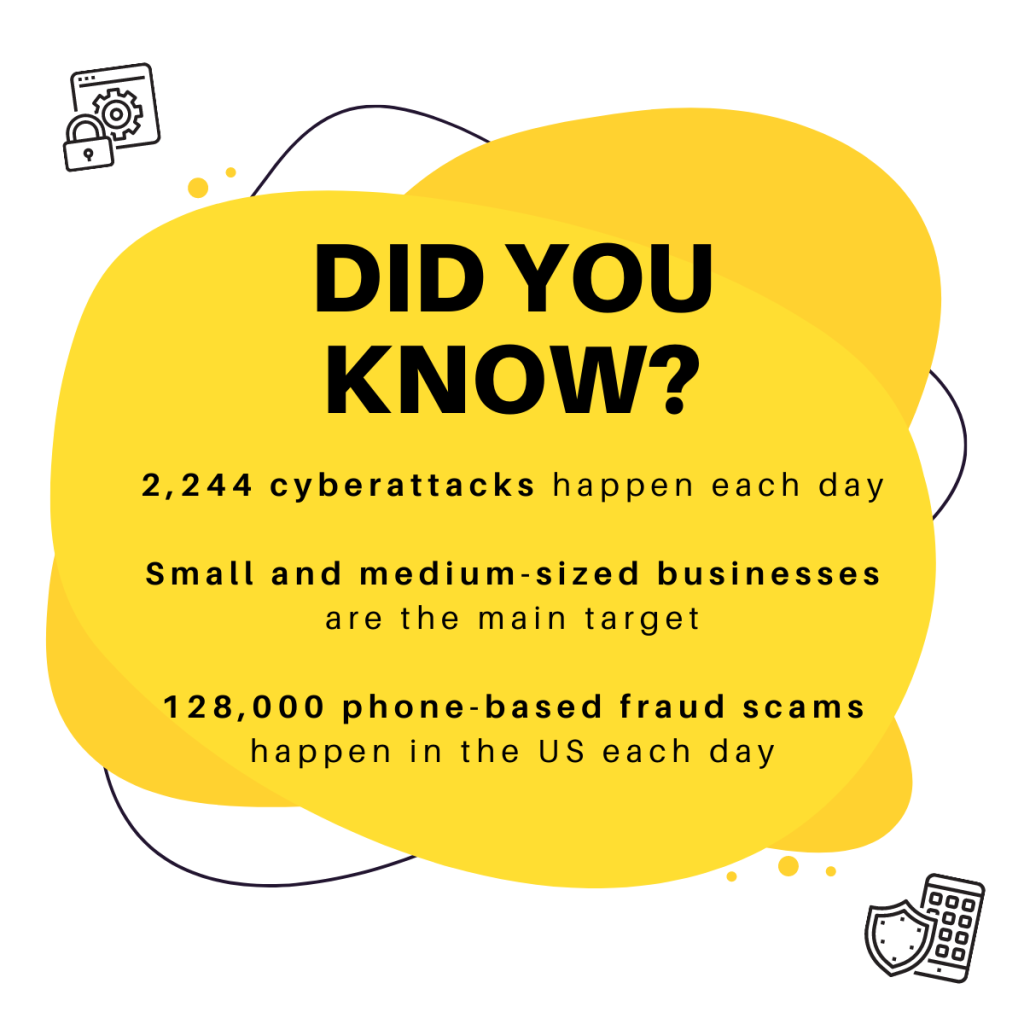
Source: KnowBe4, 2021
Hackers attack anything they see as an opportunity to make easy money or gain access to sensitive corporate data. They look for ways into networks, often through unsecured Wi-Fi connections in coffee shops or airports.
Once inside, they may use malware like ransomware to encrypt files on computers until victims pay up. Or they might try to get financial information by stealing credit card numbers or other payment details.
A report from McAfee estimated that global losses from cybercrime topped $1 trillion in 2020, and is expected to grow by 15 percent per year over the next five years, reaching $10.5 trillion annually by 2025, according to a report produced by Cybersecurity Ventures, which was sponsored by Intrusion.
So, like it or not, it’s a top priority to recognize that your business is a potential target, and cybercrime is more common than you think. The good news is there are many ways businesses can protect themselves from these threats — here are a few tips from our in-house Technology and Security expert, Mikael Vinding.
1. Multi-factor verification is key
Hacking and other techniques like phishing can be used to steal passwords and gain illegal access to your accounts. While it’s usually data breaches at large companies that grab headlines, many SMBs are left reeling from cyberattacks every year.
The first action your business can take is to set up multi-factor authentication everywhere that it’s offered. This adds extra protection to your email, team chat services, financial accounts and on mobile service providers. In fact, almost all reputable services offer this now. It is ideal to avoid using text messages for your two-factor authentication and use a security token or authenticator app if possible. That way, if a scammer gets a hold of your login, you’ve put a roadblock in place.
2. Always verify what you install
Protect yourself by always being cautious anytime you are asked to install software on your computer or device. Always verify the apps you download and make sure the software you use is from a trusted source.
Spyware allows hackers to harvest data about you and conduct surveillance on your every move. The bad guys will often target your mobile device and desktop/laptop or both, so it’s important to be vigilant on all your devices.
Malware can arrive in many ways. Be suspicious of texts and emails notifying you of updates to your favorite apps. Compromised software may contain malware or ransomware (or both) and once installed, your entire system and eventually the entire network may be at risk. Only install apps from app stores unless directed otherwise by your corporate IT department.
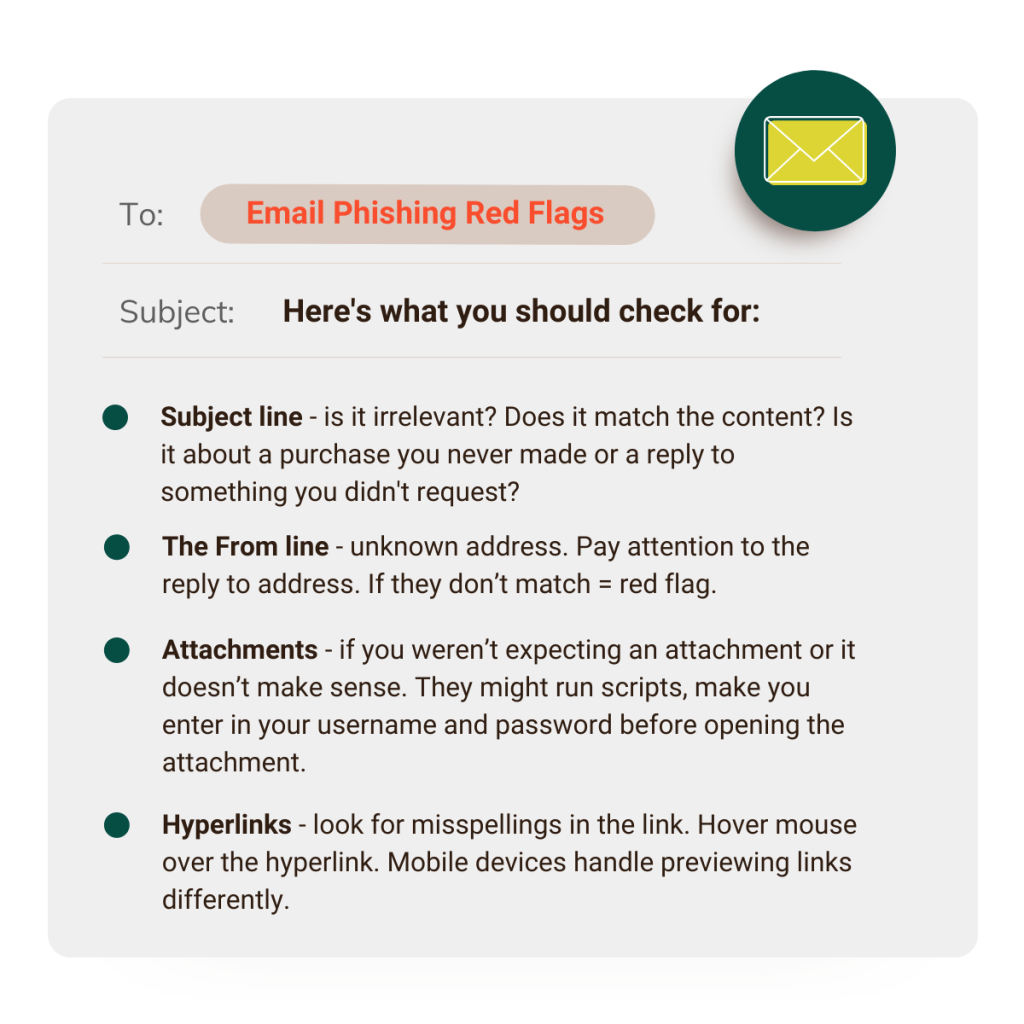
3. Beware of phishing
Phishing is when a cybercriminal attempts to acquire sensitive information, such as usernames and passwords, using bulk email that appears as if it is coming from a trusted contact or source. This attack can be very effective and has been the cause of many large data breaches.
In fact, phishing remains the top form of cybersecurity breach in 2021. Over 50% of organizations say they’ve experienced a cybersecurity breach caused by phishing (up from 51% in 2020), according to latest data from Dark Reading’s annual Strategic Security Survey.
According to the survey:
- 23% of organizations reported network disruptions and application unavailability,
- 17% say they experienced a major financial loss,
- and 15% reported fraud.
Therefore, it’s imperative to strengthen every part of your security stance, especially when it comes to phishing.
Phishing emails usually include a message that indicates an urgent threat that you need to act on right away in order to resolve the matter. For example, “Your account is going to be shut down if you don’t act fast, click here!” or “Your invoice is outstanding and will be sent to the IRS, click the attachment!”. Creating this sense of urgency is a favorite cybercriminal trick because you are more likely to make a mistake, click on an embedded link, or open something you normally would not.
The best way to combat this panic-inducing tactic? Slow down. Use a critical eye when determining whether to interact with content you receive. Double check the sender address and never respond with any sensitive information including account information. Take the extra time to verify the veracity of the communication through other channels.
4. Resist the urge to click links in sketchy emails
Phishing emails are harder than ever to spot, having become increasingly more realistic over the years. The bad guys want you to take some type of action, like clicking on a link or opening an attachment that is infected with malicious software hidden inside. Doing this will grant them access to your computer and your organization’s network.
Even if you know the sender, remember to stop, look, and think. If you receive an unexpected email saying you need to click on a link to verify an account, don’t! Instead, go directly to the institution’s website. Often, but not always, you can spot a bad link by hovering over the link and confirming if it takes you to the correct website.
5. Never (ever) provide banking information without verifying the recipient
Pretexting creates a fictional scenario where a bad actor pretends they are someone else to gain your trust and get information from you. It can happen in person, on a phone call, through text or email. It’s important to never give information over the phone, in person or online unless you have confirmed the identity. If someone is asking for specific or detailed information, politely decline.
6. Watch your social media presence
Social media can be a cybercriminal goldmine due to the reach and the ease with which information can be spread. Criminals seek out all sorts of information about you, your coworkers and your organization from your social media sites. They learn valuable information used to impersonate you or your social circle as well as learn possible answers to some common security questions, passwords and more.
Sometimes bad actors will even create fake personal or corporate profiles, use made-up scenarios to gain trust or inflict reputational and SEO damage.
Keep business and social separate and have sensible policies for employees’ use of social media. Conduct regular searches on your company and have any imposter accounts shut down.
7. Update and change your passwords
We are all told to use safe passwords all the time, but do you do it? The best thing you can do is to use a password manager and use unique passwords on all sites. Don’t forget multi factor authentication everywhere possible. Long passwords are usually better than short complicated ones. This is often called pass-phrases and are easier to type and remember but much harder to brute force attack.
Don’t use anniversaries, birthdays, pet and family member names, all that can be discovered with a quick search of your social media sites.
Final thoughts
Regardless of your company’s approach to prevention, cybersecurity is an ongoing, ever evolving threat that’s especially pernicious in the small business world. There’s no getting around it: you are a target, and cyberthreats happen much more frequently than you realize. This is why it is so important for you to remain cautious.
You play a central role in protecting your organization against the cyberthreats it faces every day. Stay alert to your surroundings, and remember to stop, look, and think before taking an action. Businesses should remain vigilant and on high-alert – especially during the tax and holiday season.
By implementing digital security measures like two-factor authentication or Bill Pay automation with tools like Checkrun, your business can easily manage your payment approval flow, and make sure that bills are not paid unless certain criteria are in place.
So, don’t procrastinate. Start implementing the cybersecurity best practices outlined above right away.
Discover how Checkrun can safeguard your business payments and ensure you are protected against payment fraud before it happens. Book a demo or contact us today!